News | November 14, 2023
DVIRC Sponsors NDIA DVC Naval Nuclear Submarine and Aircraft Carrier Supplier Conference
News | October 30, 2023
The NIST Cybersecurity Framework 2.0: Strengthening Cybersecurity for Pennsylvania
News | October 25, 2023
The U.S. Navy Commemorates Its 248th Birthday: A Legacy Born in Philadelphia
News | October 24, 2023
Announcing Shannon Fitch, DVIRC’s New Business Director of Strategic Accounts
News | October 23, 2023
Maker Spotlight: Marquita Carter, Founder of Philly Traveling Braider and TRINITY Haircare
Insights | October 23, 2023
Carly Loonstyn: Navigating the Complex World of Advanced Technology Research
News | September 25, 2023
DVIRC Shares Best Practices at the 2023 MEP National Conference: A Week of Innovation and Recognition
News | September 25, 2023
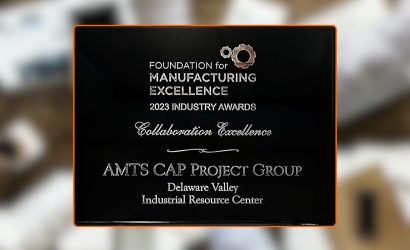
DVIRC Honored with Collaboration Excellence Award for Advancing Manufacturing Technology
[ close ]